728x90
sentry 설치
요구 사항
- Docker 19.03.6+
- Compose 1.28.0+
- 4 CPU Cores
- 8 GB RAM
- 20 GB Free Disk Space
테스트 환경
$ cat /etc/redhat-release
CentOS Linux release 7.9.2009 (Core)
$ docker --version
Docker version 19.03.13, build 4484c46d9d
$ docker-compose --version
docker-compose version 1.25.5, build 8a1c60f6docker-compose 재설치
$ curl -SsL "https://github.com/docker/compose/releases/download/1.29.2/docker-compose-$(uname -s)-$(uname -m)" -o /usr/local/bin/docker-compose
$ chmod +x /usr/local/bin/docker-compose
$ docker-compose --version
docker-compose version 1.29.2, build 5becea4csentry 설치
mkdir sentry-self-hosted
cd sentry-self-hosted/
git clone https://github.com/getsentry/self-hosted.git .
./install.sh
$ mkdir sentry-self-hosted
$ cd sentry-self-hosted/$ git clone https://github.com/getsentry/self-hosted.git .$ ./install.shWould you like to create a user account now? [Y/n]: Y
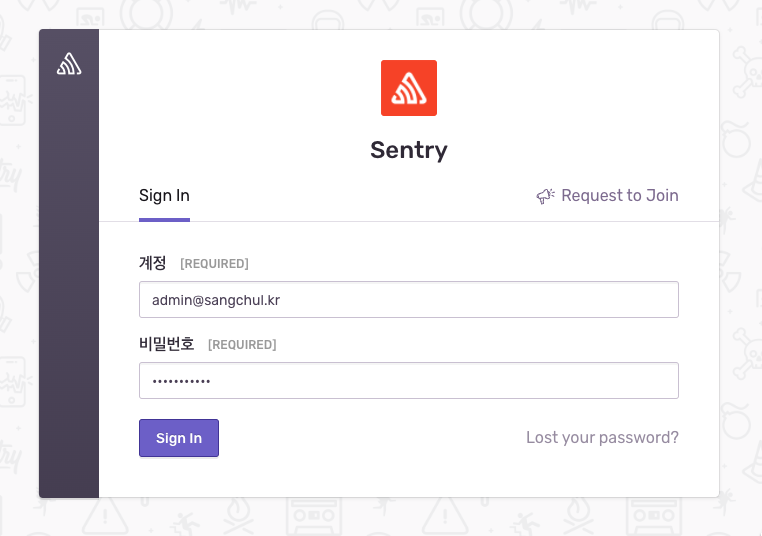
Email: admin@sangchul.kr
Password: {password}
Repeat for confirmation: {password}
Added to organization: sentry
Should this user have Super Admin role? (This grants them all permissions available) [y/N]: y
$ ./install.sh
▶ Parsing command line ...
▶ Initializing Docker Compose ...
▶ Setting up error handling ...
▶ Checking for latest commit ...
▶ Checking minimum requirements ...
Found Docker version 19.03.13
Found Docker Compose version 1.29.2
Unable to find image 'busybox:latest' locally
latest: Pulling from library/busybox
554879bb3004: Pulling fs layer
554879bb3004: Download complete
554879bb3004: Pull complete
Digest: sha256:caa382c432891547782ce7140fb3b7304613d3b0438834dce1cad68896ab110a
Status: Downloaded newer image for busybox:latest
▶ Turning things off ...
Removing network sentry-self-hosted_default
Network sentry-self-hosted_default not found.
Removing network sentry_onpremise_default
Network sentry_onpremise_default not found.
▶ Creating volumes for persistent storage ...
Created sentry-clickhouse.
Created sentry-data.
Created sentry-kafka.
Created sentry-postgres.
Created sentry-redis.
Created sentry-symbolicator.
Created sentry-zookeeper.
▶ Ensuring files from examples ...
Creating ../sentry/sentry.conf.py...
Creating ../sentry/config.yml...
Creating ../symbolicator/config.yml...
Creating ../sentry/requirements.txt...
▶ Ensuring Relay credentials ...
Creating ../relay/config.yml...
Pulling relay ...
Pulling relay ... pulling from getsentry/relay
Pulling relay ... pulling fs layer
...
...
...
...
...
Pulling relay ... status: downloaded newer image fo...
Pulling relay ... done
Creating network "sentry-self-hosted_default" with the default driver
Creating volume "sentry-self-hosted_sentry-secrets" with default driver
Creating volume "sentry-self-hosted_sentry-smtp" with default driver
Creating volume "sentry-self-hosted_sentry-zookeeper-log" with default driver
Creating volume "sentry-self-hosted_sentry-kafka-log" with default driver
Creating volume "sentry-self-hosted_sentry-smtp-log" with default driver
Creating volume "sentry-self-hosted_sentry-clickhouse-log" with default driver
Creating sentry-self-hosted_relay_run ...
Creating sentry-self-hosted_relay_run ... done
Creating sentry-self-hosted_relay_run ...
Creating sentry-self-hosted_relay_run ... done
Relay credentials written to ../relay/credentials.json.
▶ Generating secret key ...
Secret key written to ../sentry/config.yml
▶ Replacing TSDB ...
▶ Fetching and updating Docker images ...
Some service image(s) must be built from source by running:
docker-compose build symbolicator-cleanup snuba-cleanup sentry-cleanup snuba-transactions-cleanup
nightly: Pulling from getsentry/sentry
Digest: sha256:e8b4005b514b302a3c0252555be873c5706eff4f181d390ac7b973969024b229
Status: Image is up to date for getsentry/sentry:nightly
docker.io/getsentry/sentry:nightly
▶ Building and tagging Docker images ...
smtp uses an image, skipping
memcached uses an image, skipping
redis uses an image, skipping
postgres uses an image, skipping
zookeeper uses an image, skipping
kafka uses an image, skipping
clickhouse uses an image, skipping
geoipupdate uses an image, skipping
snuba-api uses an image, skipping
snuba-consumer uses an image, skipping
snuba-outcomes-consumer uses an image, skipping
snuba-sessions-consumer uses an image, skipping
snuba-transactions-consumer uses an image, skipping
snuba-replacer uses an image, skipping
snuba-subscription-consumer-events uses an image, skipping
snuba-subscription-consumer-transactions uses an image, skipping
symbolicator uses an image, skipping
web uses an image, skipping
cron uses an image, skipping
worker uses an image, skipping
ingest-consumer uses an image, skipping
post-process-forwarder uses an image, skipping
subscription-consumer-events uses an image, skipping
subscription-consumer-transactions uses an image, skipping
relay uses an image, skipping
nginx uses an image, skipping
Building snuba-cleanup
Sending build context to Docker daemon 3.584kB
Step 1/5 : ARG BASE_IMAGE
Step 2/5 : FROM ${BASE_IMAGE}
...
...
...
...
...
Removing intermediate container 1c3496ca25d4
---> 5f66669dae32
Successfully built 5f66669dae32
Successfully tagged sentry-cleanup-self-hosted-local:latest
Docker images built.
▶ Setting up Zookeeper ...
Creating sentry-self-hosted_zookeeper_run ...
Creating sentry-self-hosted_zookeeper_run ... done
▶ Downloading and installing wal2json ...
Unable to find image 'curlimages/curl:7.77.0' locally
7.77.0: Pulling from curlimages/curl
339de151aab4: Already exists
9576f9a419e9: Pulling fs layer
5b67e0e9bce9: Pulling fs layer
7c0640a6c519: Pulling fs layer
...
...
...
...
...
Applying sessions.0001_initial... OK
Applying sites.0001_initial... OK
Applying sites.0002_alter_domain_unique... OK
Applying social_auth.0001_initial... OK
12:34:32 [WARNING] sentry: Cannot initiate onboarding for organization (1) due to missing owners
Created internal Sentry project (slug=internal, id=1)
Would you like to create a user account now? [Y/n]: Y
Email: admin@sangchul.kr
Password:
Repeat for confirmation:
Added to organization: sentry
Should this user have Super Admin role? (This grants them all permissions available) [y/N]: y
User created: admin@sangchul.kr
Creating missing DSNs
Correcting Group.num_comments counter
▶ Migrating file storage ...
Unable to find image 'alpine:latest' locally
latest: Pulling from library/alpine
3aa4d0bbde19: Already exists
Digest: sha256:ceeae2849a425ef1a7e591d8288f1a58cdf1f4e8d9da7510e29ea829e61cf512
Status: Downloaded newer image for alpine:latest
▶ Setting up GeoIP integration ...
Setting up IP address geolocation ...
Installing (empty) IP address geolocation database ... done.
IP address geolocation is not configured for updates.
See https://develop.sentry.dev/self-hosted/geolocation/ for instructions.
Error setting up IP address geolocation.
-----------------------------------------------------------------
You're all done! Run the following command to get Sentry running:
docker-compose up -d
-----------------------------------------------------------------728x90
이미지 리스트
$ docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
sentry-cleanup-self-hosted-local latest 5f66669dae32 15 minutes ago 1.06GB
symbolicator-cleanup-self-hosted-local latest 9865b2aa0245 15 minutes ago 141MB
snuba-cleanup-self-hosted-local latest 6c9118dc6dba 15 minutes ago 453MB
getsentry/sentry nightly 5f526b82b022 36 minutes ago 1.06GB
getsentry/snuba nightly ae7ee75c56da 13 hours ago 452MB
nginx 1.21.6-alpine d7c7c5df4c3a 19 hours ago 23.4MB
alpine latest 9c842ac49a39 21 hours ago 5.57MB
getsentry/symbolicator nightly 05db6bbb5bb4 2 days ago 140MB
tianon/exim4 latest fced99e99060 7 days ago 158MB
getsentry/relay nightly 8ec1391bf448 8 days ago 217MB
busybox latest 2fb6fc2d97e1 12 days ago 1.24MB
postgres 9.6 027ccf656dc1 5 weeks ago 200MB
allinurl/goaccess latest 600982f2be96 7 weeks ago 15.4MB
elasticsearch 7.10.2-log4j-2.15.0 0a51d980c9d8 3 months ago 898MB
certbot/certbot latest 6ddd9ccfe97c 3 months ago 111MB
nginx latest f652ca386ed1 3 months ago 141MB
confluentinc/cp-kafka 5.5.0 efc480c1c89c 5 months ago 598MB
confluentinc/cp-zookeeper 5.5.0 ddeb961d8e80 5 months ago 598MB
redis 6.2.4-alpine 500703a12fa4 8 months ago 32.3MB
memcached 1.6.9-alpine a0132b3398e4 9 months ago 8.09MB
ngrinder/agent latest b53a24599fae 9 months ago 171MB
ngrinder/controller latest 6f188a40b907 9 months ago 454MB
curlimages/curl 7.77.0 e062233fb4a9 10 months ago 8.26MB
maxmindinc/geoipupdate v4.7.1 8ec32cc727c7 11 months ago 10.6MB
cyberduck/php-fpm-laravel latest bbc7dc5f6071 12 months ago 739MB
docker.elastic.co/elasticsearch/elasticsearch 7.10.2 0b58e1cea500 14 months ago 814MB
yandex/clickhouse-server 20.3.9.70 abe55fc6544d 22 months ago 497MBdocker-compose up -d
$ docker-compose up -d
Starting sentry-self-hosted_symbolicator_1 ... done
Starting sentry-self-hosted_redis_1 ... done
Starting sentry-self-hosted_memcached_1 ... done
Starting sentry-self-hosted_clickhouse_1 ... done
Starting sentry-self-hosted_postgres_1 ... done
Starting sentry-self-hosted_smtp_1 ... done
Starting sentry-self-hosted_zookeeper_1 ... done
Creating sentry-self-hosted_symbolicator-cleanup_1 ... done
Creating sentry-self-hosted_geoipupdate_1 ... done
Starting sentry-self-hosted_kafka_1 ... done
Starting sentry-self-hosted_snuba-outcomes-consumer_1 ... done
Creating sentry-self-hosted_snuba-cleanup_1 ... done
Starting sentry-self-hosted_snuba-subscription-consumer-transactions_1 ... done
Starting sentry-self-hosted_snuba-api_1 ... done
Starting sentry-self-hosted_snuba-replacer_1 ... done
Starting sentry-self-hosted_snuba-sessions-consumer_1 ... done
Starting sentry-self-hosted_snuba-consumer_1 ... done
Starting sentry-self-hosted_snuba-subscription-consumer-events_1 ... done
Creating sentry-self-hosted_snuba-transactions-cleanup_1 ... done
Starting sentry-self-hosted_snuba-transactions-consumer_1 ... done
Creating sentry-self-hosted_sentry-cleanup_1 ... done
Creating sentry-self-hosted_cron_1 ... done
Creating sentry-self-hosted_web_1 ... done
Creating sentry-self-hosted_subscription-consumer-transactions_1 ... done
Creating sentry-self-hosted_worker_1 ... done
Creating sentry-self-hosted_ingest-consumer_1 ... done
Creating sentry-self-hosted_subscription-consumer-events_1 ... done
Creating sentry-self-hosted_post-process-forwarder_1 ... done
Creating sentry-self-hosted_relay_1 ... done
Creating sentry-self-hosted_nginx_1 ... donedocker-compose ps
$ docker-compose ps
Name Command State Ports
--------------------------------------------------------------------------------------------------------------------------------------------
sentry-self-hosted_clickhouse_1 /entrypoint.sh Up (healthy) 8123/tcp, 9000/tcp, 9009/tcp
sentry-self-hosted_cron_1 /etc/sentry/entrypoint.sh ... Up 9000/tcp
sentry-self-hosted_geoipupdate_1 /usr/bin/geoipupdate -d /s ... Exit 1
sentry-self-hosted_ingest-consumer_1 /etc/sentry/entrypoint.sh ... Up 9000/tcp
sentry-self-hosted_kafka_1 /etc/confluent/docker/run Up (healthy) 9092/tcp
sentry-self-hosted_memcached_1 docker-entrypoint.sh memcached Up (healthy) 11211/tcp
sentry-self-hosted_nginx_1 /docker-entrypoint.sh ngin ... Up 0.0.0.0:9000->80/tcp
sentry-self-hosted_post-process-forwarder_1 /etc/sentry/entrypoint.sh ... Up 9000/tcp
sentry-self-hosted_postgres_1 /opt/sentry/postgres-entry ... Up (healthy) 5432/tcp
sentry-self-hosted_redis_1 docker-entrypoint.sh redis ... Up (healthy) 6379/tcp
sentry-self-hosted_relay_1 /bin/bash /docker-entrypoi ... Up 3000/tcp
sentry-self-hosted_sentry-cleanup_1 /entrypoint.sh 0 0 * * * g ... Up 9000/tcp
sentry-self-hosted_smtp_1 docker-entrypoint.sh exim ... Up 25/tcp
sentry-self-hosted_snuba-api_1 ./docker_entrypoint.sh api Up 1218/tcp
sentry-self-hosted_snuba-cleanup_1 /entrypoint.sh */5 * * * * ... Up 1218/tcp
sentry-self-hosted_snuba-consumer_1 ./docker_entrypoint.sh con ... Up 1218/tcp
sentry-self-hosted_snuba-outcomes-consumer_1 ./docker_entrypoint.sh con ... Up 1218/tcp
sentry-self-hosted_snuba-replacer_1 ./docker_entrypoint.sh rep ... Up 1218/tcp
sentry-self-hosted_snuba-sessions-consumer_1 ./docker_entrypoint.sh con ... Up 1218/tcp
sentry-self-hosted_snuba-subscription-consumer-events_1 ./docker_entrypoint.sh sub ... Up 1218/tcp
sentry-self-hosted_snuba-subscription-consumer-transactions_1 ./docker_entrypoint.sh sub ... Up 1218/tcp
sentry-self-hosted_snuba-transactions-cleanup_1 /entrypoint.sh */5 * * * * ... Up 1218/tcp
sentry-self-hosted_snuba-transactions-consumer_1 ./docker_entrypoint.sh con ... Up 1218/tcp
sentry-self-hosted_subscription-consumer-events_1 /etc/sentry/entrypoint.sh ... Up 9000/tcp
sentry-self-hosted_subscription-consumer-transactions_1 /etc/sentry/entrypoint.sh ... Up 9000/tcp
sentry-self-hosted_symbolicator-cleanup_1 /entrypoint.sh 55 23 * * * ... Up 3021/tcp
sentry-self-hosted_symbolicator_1 /bin/bash /docker-entrypoi ... Up 3021/tcp
sentry-self-hosted_web_1 /etc/sentry/entrypoint.sh ... Up (healthy) 9000/tcp
sentry-self-hosted_worker_1 /etc/sentry/entrypoint.sh ... Up 9000/tcp
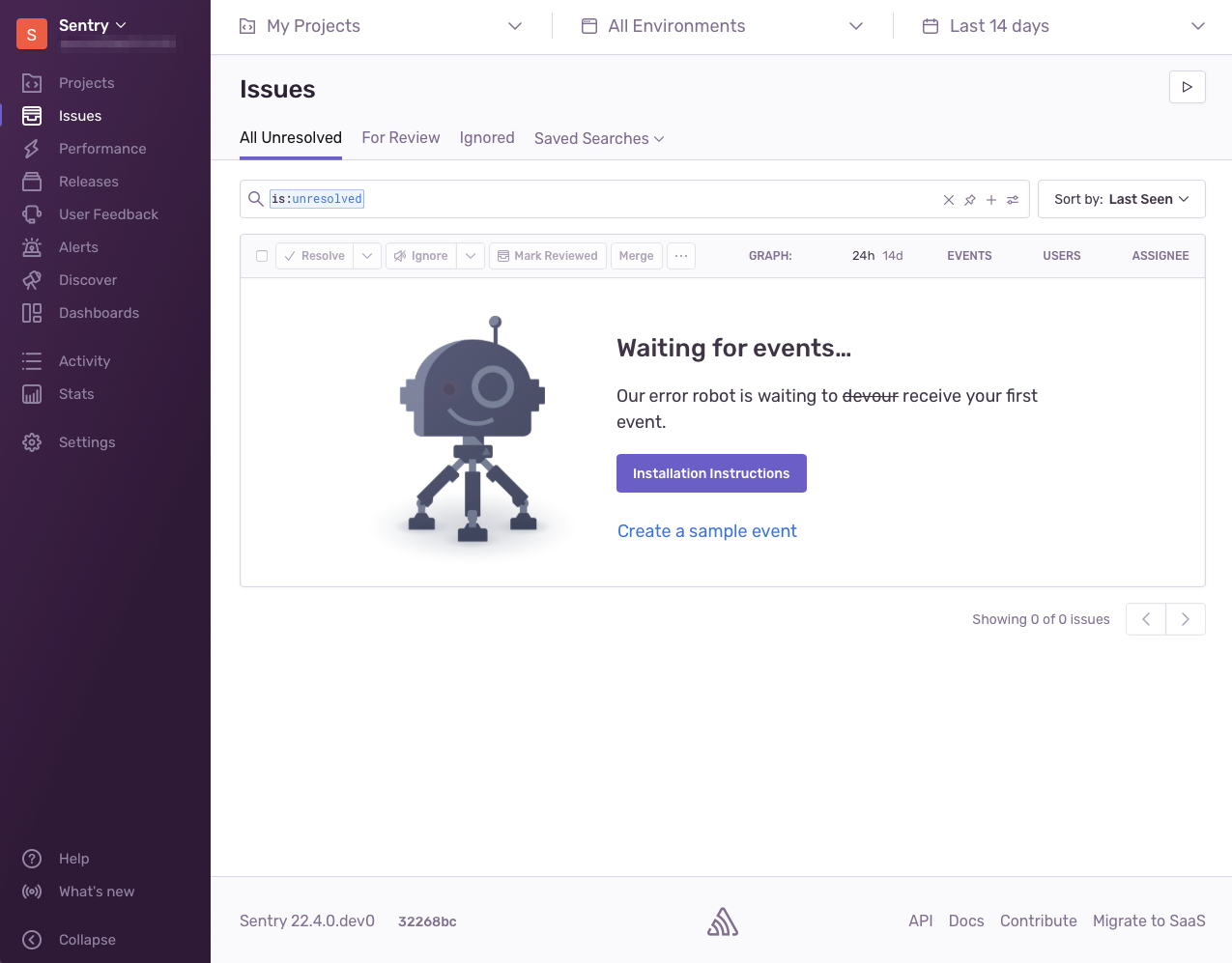
sentry-self-hosted_zookeeper_1 /etc/confluent/docker/run Up (healthy) 2181/tcp, 2888/tcp, 3888/tcphttp://{SERVER IP}:9000
계정 : admin@sangchul.kr
비밀번호 : password

728x90
'리눅스' 카테고리의 다른 글
| [리눅스] private docker registry 사용 방법 (0) | 2022.03.28 |
|---|---|
| CentOS 7에 Node.js와 npm을 설치하는 방법 (0) | 2022.03.25 |
| CentOS 7에서 ISO 이미지를 생성하기(mkisofs) (0) | 2022.03.24 |
| 병렬 압축 - parallel compression (0) | 2022.03.24 |
| [보안취약점] 리눅스 계정 잠금 임계값 설정 (0) | 2022.03.24 |



