원도우 11에서 Docker Desktop을 설치하는 방법
Docker Desktop은 Windows용 Docker 애플리케이션으로, Windows 11에서도 사용할 수 있습니다.
참고: Windows 11을 실행하는 컴퓨터는 하드웨어 가상화 기능(VT-x/AMD-v)이 활성화되어 있어야 합니다.
1. 먼저 Docker Desktop을 다운로드합니다. 아래 링크에서 Windows 용 Docker Desktop을 다운로드하세요. https://www.docker.com/products/docker-desktop
2. 다운로드한 설치 파일을 실행합니다.
3. 설치 중에 시스템에 Hyper-V 기능이 활성화되어 있는지 확인합니다. Docker Desktop은 Hyper-V를 사용하여 가상화를 수행합니다.
4. 설치가 완료되면 Docker Desktop을 실행합니다. 처음 실행할 때 Docker Desktop이 하이퍼바이저(Hyper-V)를 사용하도록 허용하라는 메시지가 나타날 수 있습니다. 이에 동의합니다.

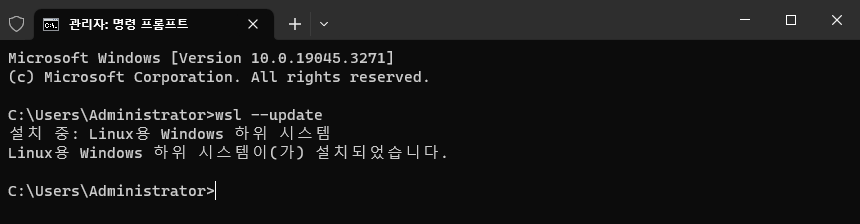
wsl --update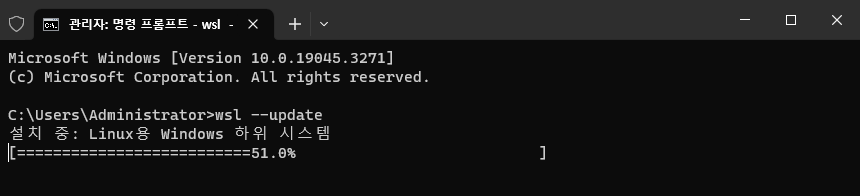
5. Docker Desktop이 실행되면 시스템 트레이에 Docker 아이콘이 나타납니다. 이제 Docker를 사용하여 컨테이너를 생성하고 관리할 수 있습니다.

6. 컨테이너를 생성하려면 Docker 이미지를 사용합니다. Docker Hub(https://hub.docker.com/)에서 여러 이미지를 찾아볼 수 있으며, docker pull 명령을 사용하여 이미지를 다운로드할 수 있습니다.
7. 컨테이너를 생성하고 실행하려면 docker run 명령어를 사용합니다. 예를 들어, 아래 명령어는 "hello-world" 이미지를 실행하는 컨테이너를 생성합니다.
docker run hello-world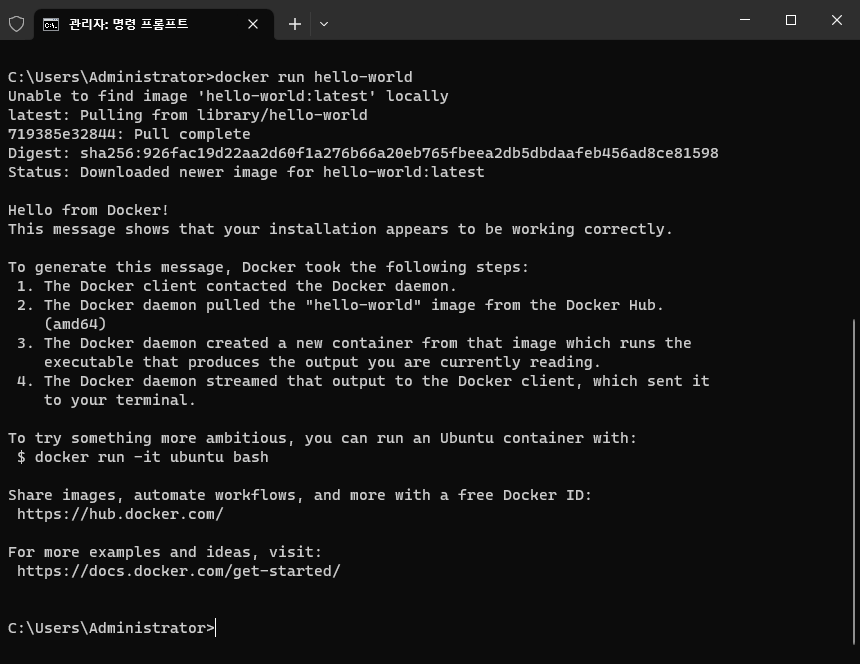
위와 같이 실행하면 컨테이너가 생성되고 "Hello from Docker!"와 같은 출력을 확인할 수 있습니다.
docker 사용법
>docker --help
Usage: docker [OPTIONS] COMMAND
A self-sufficient runtime for containers
Common Commands:
run Create and run a new container from an image
exec Execute a command in a running container
ps List containers
build Build an image from a Dockerfile
pull Download an image from a registry
push Upload an image to a registry
images List images
login Log in to a registry
logout Log out from a registry
search Search Docker Hub for images
version Show the Docker version information
info Display system-wide information
Management Commands:
builder Manage builds
buildx* Docker Buildx (Docker Inc., v0.11.2-desktop.1)
compose* Docker Compose (Docker Inc., v2.20.2-desktop.1)
container Manage containers
context Manage contexts
dev* Docker Dev Environments (Docker Inc., v0.1.0)
extension* Manages Docker extensions (Docker Inc., v0.2.20)
image Manage images
init* Creates Docker-related starter files for your project (Docker Inc., v0.1.0-beta.6)
manifest Manage Docker image manifests and manifest lists
network Manage networks
plugin Manage plugins
sbom* View the packaged-based Software Bill Of Materials (SBOM) for an image (Anchore Inc., 0.6.0)
scan* Docker Scan (Docker Inc., v0.26.0)
scout* Command line tool for Docker Scout (Docker Inc., 0.20.0)
system Manage Docker
trust Manage trust on Docker images
volume Manage volumes
Swarm Commands:
swarm Manage Swarm
Commands:
attach Attach local standard input, output, and error streams to a running container
commit Create a new image from a container's changes
cp Copy files/folders between a container and the local filesystem
create Create a new container
diff Inspect changes to files or directories on a container's filesystem
events Get real time events from the server
export Export a container's filesystem as a tar archive
history Show the history of an image
import Import the contents from a tarball to create a filesystem image
inspect Return low-level information on Docker objects
kill Kill one or more running containers
load Load an image from a tar archive or STDIN
logs Fetch the logs of a container
pause Pause all processes within one or more containers
port List port mappings or a specific mapping for the container
rename Rename a container
restart Restart one or more containers
rm Remove one or more containers
rmi Remove one or more images
save Save one or more images to a tar archive (streamed to STDOUT by default)
start Start one or more stopped containers
stats Display a live stream of container(s) resource usage statistics
stop Stop one or more running containers
tag Create a tag TARGET_IMAGE that refers to SOURCE_IMAGE
top Display the running processes of a container
unpause Unpause all processes within one or more containers
update Update configuration of one or more containers
wait Block until one or more containers stop, then print their exit codes
Global Options:
--config string Location of client config files (default
"C:\\Users\\Administrator\\.docker")
-c, --context string Name of the context to use to connect to the
daemon (overrides DOCKER_HOST env var and
default context set with "docker context use")
-D, --debug Enable debug mode
-H, --host list Daemon socket to connect to
-l, --log-level string Set the logging level ("debug", "info",
"warn", "error", "fatal") (default "info")
--tls Use TLS; implied by --tlsverify
--tlscacert string Trust certs signed only by this CA (default
"C:\\Users\\Administrator\\.docker\\ca.pem")
--tlscert string Path to TLS certificate file (default
"C:\\Users\\Administrator\\.docker\\cert.pem")
--tlskey string Path to TLS key file (default
"C:\\Users\\Administrator\\.docker\\key.pem")
--tlsverify Use TLS and verify the remote
-v, --version Print version information and quit
Run 'docker COMMAND --help' for more information on a command.
For more help on how to use Docker, head to https://docs.docker.com/go/guides/
Docker Desktop을 설치하고 실행하면 이제 Windows 11에서 컨테이너 기반의 응용 프로그램을 구축, 실행 및 관리할 수 있습니다. Docker에 익숙하지 않은 경우 Docker 문서와 사용자 가이드를 참조하여 더 자세히 알아보시기 바랍니다.
'원도우' 카테고리의 다른 글
| [draft] 원도우에서 "프록시 설정" 바로 가기 만들기 (0) | 2026.01.05 |
|---|---|
| [draft] "Microsoft.PowerShell_profile.ps1 파일을 로드할 수 없습니다." 오류 (0) | 2025.12.10 |
| [draft] Windows에서 패스워드를 변경하는 방법 (0) | 2025.12.09 |
| [WIP] 원도우 11에서 로컬 보안 정책과 그룹 정책을 통한 암호 정책 설정 방법 (0) | 2025.12.09 |
| [draft] 윈도우11 버전 확인 방법 (0) | 2025.12.09 |



