728x90
Vault 클러스터를 Consul을 백엔드 스토리지로 사용하여 구성하는 방법
1. Consul 클러스터 설정
Consul 설정 파일
- retry_join 항목에 클러스터 내 다른 Consul 서버들의 IP를 입력합니다. 각 서버마다 node_name과 IP 주소를 고유하게 설정합니다.
vim /etc/consul.d/consul.hcldatacenter = "dc1"
data_dir = "/opt/consul"
log_level = "INFO"
node_name = "consul-server-1" # 각 서버마다 고유하게 설정
server = true
bootstrap_expect = 3 # 클러스터 내 서버 수
bind_addr = "0.0.0.0"
client_addr = "0.0.0.0"
retry_join = ["<consul_server_1_ip>", "<consul_server_2_ip>", "<consul_server_3_ip>"]2. Vault 설치 및 설정
Vault 설정 파일
- /etc/vault.d/vault.hcl 파일을 작성합니다.
vim /etc/vault.d/vault.hclstorage "consul" {
address = "http://<consul_server_1_ip>:8500"
path = "vault/"
}
listener "tcp" {
address = "0.0.0.0:8200"
tls_disable = 1
}
api_addr = "http://<vault_node_ip>:8200"
cluster_addr = "http://<vault_node_ip>:8201"- node211
sudo tee /etc/vault.d/vault.hcl > /dev/null <<EOF
ui = true
storage "consul" {
address = "http://192.168.0.211:8500"
path = "vault/"
}
listener "tcp" {
address = "0.0.0.0:8200"
tls_disable = 1
}
api_addr = "http://192.168.0.211:8200"
cluster_addr = "http://192.168.0.211:8201"
EOF- node212
sudo tee /etc/vault.d/vault.hcl > /dev/null <<EOF
ui = true
storage "consul" {
address = "http://192.168.0.212:8500"
path = "vault/"
}
listener "tcp" {
address = "0.0.0.0:8200"
tls_disable = 1
}
api_addr = "http://192.168.0.212:8200"
cluster_addr = "http://192.168.0.212:8201"
EOF- node213
sudo tee /etc/vault.d/vault.hcl > /dev/null <<EOF
ui = true
storage "consul" {
address = "http://192.168.0.213:8500"
path = "vault/"
}
listener "tcp" {
address = "0.0.0.0:8200"
tls_disable = 1
}
api_addr = "http://192.168.0.213:8200"
cluster_addr = "http://192.168.0.213:8201"
EOFsudo systemctl restart vaultsudo systemctl status vault --no-pager3. Vault 초기화 및 클러스터 구성
Vault 초기화
클러스터의 첫 번째 서버에서 Vault를 초기화합니다.
vault operator init | tee ~/vault_info.txt$ vault operator init
Unseal Key 1: r8c5QcvtcqrEAQKX/mo/Mnc4Omx4jHa1G2Ljnu/y4I8u
Unseal Key 2: biF07mWmcDAP3lcImG6r1ztvAtYEDeB6zb0Y83iCnlmq
Unseal Key 3: rs8SdERte+jfvvgL8qc5J/OZGv1XixGaAZsnp9SzrUOA
Unseal Key 4: vbcAJWv6FZqvRm74kHQ0Bbbc0EZOcixWuIjWDvpDBV+k
Unseal Key 5: GEVFLOcAVshPjS4bg6RA/6CO8feuEh3PuMpuSl0PsnfJ
Initial Root Token: hvs.BIxTB1s1qVzlFPWat5FxbfKy
Vault initialized with 5 key shares and a key threshold of 3. Please securely
distribute the key shares printed above. When the Vault is re-sealed,
restarted, or stopped, you must supply at least 3 of these keys to unseal it
before it can start servicing requests.
Vault does not store the generated root key. Without at least 3 keys to
reconstruct the root key, Vault will remain permanently sealed!
It is possible to generate new unseal keys, provided you have a quorum of
existing unseal keys shares. See "vault operator rekey" for more information.환경 변수 설정
export VAULT_ADDR='http://127.0.0.1:8200'export VAULT_TOKEN="hvs.BIxTB1s1qVzlFPWat5FxbfKy"언실(Sealing) 해제
초기화된 Vault를 언실하기 위해 언실 키를 사용합니다.
vault operator unseal <unseal_key>vault operator unseal r8c5QcvtcqrEAQKX/mo/Mnc4Omx4jHa1G2Ljnu/y4I8u
vault operator unseal biF07mWmcDAP3lcImG6r1ztvAtYEDeB6zb0Y83iCnlmq
vault operator unseal rs8SdERte+jfvvgL8qc5J/OZGv1XixGaAZsnp9SzrUOA
vault login <root_token>vault login$ vault login
Token (will be hidden):
WARNING! The VAULT_TOKEN environment variable is set! The value of this
variable will take precedence; if this is unwanted please unset VAULT_TOKEN or
update its value accordingly.
Success! You are now authenticated. The token information displayed below
is already stored in the token helper. You do NOT need to run "vault login"
again. Future Vault requests will automatically use this token.
Key Value
--- -----
token hvs.BIxTB1s1qVzlFPWat5FxbfKy
token_accessor Yv6MJeWTkWwRvCKHG7JCZ1qU
token_duration ∞
token_renewable false
token_policies ["root"]
identity_policies []
policies ["root"]
vault operator members$ vault operator members
Host Name API Address Cluster Address Active Node Version Upgrade Version Redundancy Zone Last Echo
--------- ----------- --------------- ----------- ------- --------------- --------------- ---------
node211 http://192.168.0.211:8200 https://192.168.0.211:8201 true 1.17.2 n/a n/a n/a클러스터에 노드 추가
export VAULT_ADDR='http://192.168.0.211:8200'export VAULT_TOKEN="hvs.6j4cuewowBGit65rheNoceI7"나머지 서버에서 첫 번째 서버에 연결하여 클러스터에 참여시킵니다.
vault operator raft join http://<첫_번째_서버_ip>:8200vault operator raft join http://192.168.0.211:8200각 노드 언실(Sealing) 해제
- 클러스터에 참여한 각 노드를 언실합니다.
vault operator unseal <unseal_key>vault operator unseal r8c5QcvtcqrEAQKX/mo/Mnc4Omx4jHa1G2Ljnu/y4I8u
vault operator unseal biF07mWmcDAP3lcImG6r1ztvAtYEDeB6zb0Y83iCnlmq
vault operator unseal rs8SdERte+jfvvgL8qc5J/OZGv1XixGaAZsnp9SzrUOA
vault login $VAULT_TOKEN
vault operator members$ vault operator members
Host Name API Address Cluster Address Active Node Version Upgrade Version Redundancy Zone Last Echo
--------- ----------- --------------- ----------- ------- --------------- --------------- ---------
node211 http://192.168.0.211:8200 https://192.168.0.211:8201 true 1.17.2 n/a n/a n/a
node212 http://192.168.0.212:8200 https://192.168.0.212:8201 false 1.17.2 n/a n/a 2024-07-26T11:04:04+09:00
node213 http://192.168.0.213:8200 https://192.168.0.213:8201 false 1.17.2 n/a n/a 2024-07-26T11:04:07+09:00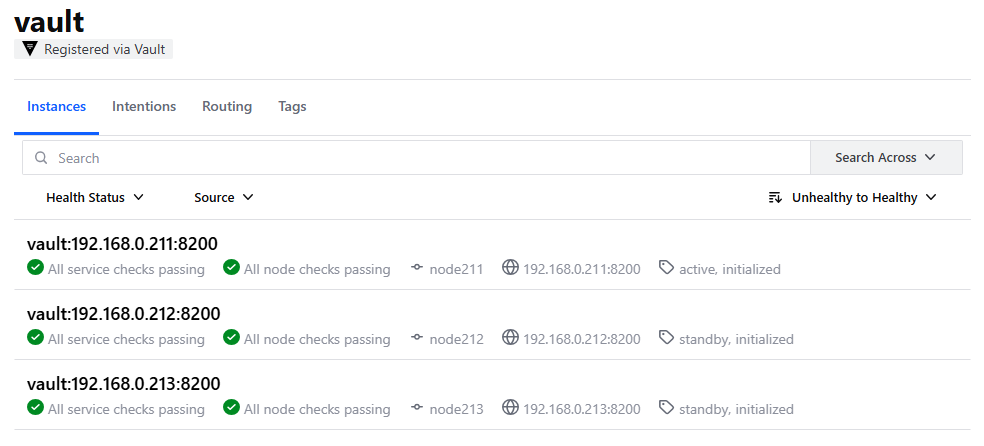
4. 클러스터 상태 확인
모든 서버에서 vault status 명령어를 사용하여 클러스터 상태를 확인합니다.
vault status$ vault status
Key Value
--- -----
Seal Type shamir
Initialized true
Sealed false
Total Shares 5
Threshold 3
Version 1.17.2
Build Date 2024-07-05T15:19:12Z
Storage Type consul
Cluster Name vault-cluster-3f170889
Cluster ID deb82303-0680-7690-fded-86c3bda98907
HA Enabled true
HA Cluster https://192.168.0.211:8201
HA Mode active
Active Since 2024-07-25T16:24:31.756581423+09:00
정상적으로 클러스터가 구성되었다면 각 서버에서 Vault의 상태 정보를 확인할 수 있습니다.
sudo tee /etc/vault.d/vault.hcl > /dev/null <<EOF ui = true Storage "consul" { address = "http://192.168.0.213:8500" path = "vault/" } Listener " tcp" { 주소 = "0.0.0.0:8200" tls_disable = 1 } api_addr = "http://192.168.0.213:8200" Cluster_addr = "http://192.168.0.213:8201" EOF
728x90
'리눅스' 카테고리의 다른 글
| [draft] Vault를 사용하여 SSH CA 키를 관리하는 방법 (0) | 2024.07.29 |
|---|---|
| [draft] 우분투에서 사용자별 용량 제한을 설정하고 사용하는 방법 (0) | 2024.07.28 |
| [draft] 우분투에 HashiCorp Vault를 설치하고 클러스터를 구성하는 방법 (0) | 2024.07.24 |
| [draft] 쿠버네티스 클러스터를 고가용성으로 구성하는 방법 (0) | 2024.07.23 |
| [draft] etcd 클러스터를 구성하는 방법 (0) | 2024.07.23 |



